- ISC2 Community
- :
- Discussions
- :
- Industry News
- :
- o/' Mem'ries ... o/'
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The CISSPforum History of Infosec InSecurity
Over on the CISSPforum, there is an interesting project going on. (Well, I find it interesting, anyway. And I'm the one who's making this post.)
The old-timers are looking back into the dim recesses of their fading memories, and trying to recall, before we all die or go senile, seminal moments in infosec history.
I'll try and remember (if I don't wonder out into the street and get hit by a bus) to post some of them here.
............
Other posts: https://community.isc2.org/t5/forums/recentpostspage/user-id/1324864413
This message may or may not be governed by the terms of
http://www.noticebored.com/html/cisspforumfaq.html#Friday or
https://blogs.securiteam.com/index.php/archives/1468
- Labels:
-
Information Security
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'll include the AIDS Information Disk trojan/ransomware for three reasons:
1. It deserves a place in the history of malware.
2. It was so widely, and incorrectly, reported as a virus.
3. It used the HIV/AIDS scare to get people to use it.
In the fall of 1989, about 10,000 copies of an "AIDS Information" package were sent out from a company calling itself PC Cyborg. Some were received at medical establishments; a number were received at other types of businesses, mostly in Britain and Europe. The packages appeared to have been professionally produced. (And anything professional/commercial is OK, right?)
Accompanying letters usually referred to them as sample or review copies. However, the packages also contained a very interesting "license agreement": "In case of breach of license, PC Cyborg Corporation reserves the right to use program mechanisms to ensure termination of the use of these programs. These program mechanisms will adversely affect other program applications on microcomputers. You are hereby advised of the most serious consequences of your failure to abide by the terms of this license agreement." Further in the license is the sentence: "Warning: Do not use these programs unless you are prepared to pay for them." From what followed, it seems likely that "PC Cyborg" meant to use this agreement as a legal defence if anything went wrong. In the end, that wasn't tested in court.
The disks contained an installation program and a very simplistic AIDS information "page turner" and risk assessment program. The installation program appeared only to copy the AIDS program onto the target hard disk, but in reality did much more. A hidden directory was created with a nonprinting character name, and a hidden program file with a nonprinting character in the name was installed. The AUTOEXEC.BAT file (you remember AUTOEXEC.BAT, don't you?) was renamed and replaced with one that called the hidden program and then the original AUTOEXEC. The hidden program kept track of the number of times the computer was rebooted, and, after a certain number, encrypted the hard disk. The user was then presented with an invoice and a demand to pay the license fee in return for the encryption/decryption key. (No asymmetric algorithms for us. Real blackhats use symmetric encryption!)
Two major "versions" were found to have been shipped. One, which waited for 90 reboots, was thought to be the "real" attempt: an earlier version, which encrypted after one reboot, alerted authorities fairly early, and it's inclusion or sending was thought to be an error on the part of the principals of PC Cyborg.
The Panamanian address for PC Cyborg, thought by some to be a fake, turned out to be real. Four principals were identified, as well as an American accomplice who seems to have had plans to send 200,000 copies to American firms if the European "test" worked. The trial of the American (a Dr. Joseph Popp) was suspended in Britain, as his bizarre behaviour in court was seen as an indication that he was unfit to plead. An Italian court, however, found him guilty and sentenced him in absentia.
............
Other posts: https://community.isc2.org/t5/forums/recentpostspage/user-id/1324864413
This message may or may not be governed by the terms of
http://www.noticebored.com/html/cisspforumfaq.html#Friday or
https://blogs.securiteam.com/index.php/archives/1468
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Well, these aren't exactly major milestones in infosec history, but thinking about recounting history brought the issues back to me. And they make points about our reliance on the sales and marketing aspects of our industry, and on some of our tech tools, even when they make no sense.
A reasonably prominent periodical devoted to security topics had been advertising for writers in, among other areas, the virus field, so I sent some sample materials off. (They were even willing to pay!) I did not hear anything for about eight months, and then I got a call asking me to do an article. Not on viruses. On groupware. Well, I've been doing collaborative work on the net forever, and I did, at one time, some government contracting involving reviewing this type of software, so, why not?
However, it was not enough to write the article. No, I had to contact the vendors and listen to what they had to say on the topic. This actually consumed the most time. (You've all had to listen to vendors. You'll know why ...) Some research, and some roughing out an outline: two hours. A rough draft: three. Polishing the final draft: an hour. Lots of room for profit there. (Of course, when you consider the years it took to build the background to be able to do that, it tends to reduce the margin a bit....) But contacting three consultants, two user-group representatives, and eleven representatives from seven major vendors ... ? In the end it got me one very helpful vendor contact, one returned message, one faxed spec sheet from a loosely related product, and a heavy parcel, which arrived postage due after the deadline. Needless to say, this was less than helpful to the project.
In the end, the article was rejected. Not enough "vendor quotes."
What is really important here is the fact that most of the articles being generated in the trade press are, by and large, "infomercials" on the printed page. Articles are being written by people who, if they have a technical background at all, are writing out of their field and are being judged on the acceptability of the content to vendors and advertisers. The vendors don't care about quality as long as a) you spell the name of their product correctly, and b) don't raise any issues that might reflect negatively on their product.
On another occasion, I was asked to turn out an article on, of all things, computer viruses! Be still my beating heart! I get to write in my field, about things I actually understand! I was, of course, asked because a search of the net turns up all kinds of articles that I've written. (Going back many, many years.)
In this case, the publisher wanted graphics. Lots of pictures. Well, I don't do graphics. I do text. I research. I delve. I push. I don't spend my time thinking up clever ways to illustrate a story about the Michelangelo virus with a parody of the ceiling of the Sistine Chapel, particularly since Michelangelo had nothing to do with the virus except that it triggered on his birthday. (And that was only found out by chance ...)
But I spend hours and hours trying to think up graphics that were actually suitable to the article, and create (or steal) them.
And then that article was turned down, too!
Why? Well, the company had this new plagiarism tool, that checked submitted content against the net. And, lo and behold, it turns out there were a lot of articles on the net, that talked about viruses in a way that was very similar to what I did. Well, of course there were. I wrote them! But, the tool said it was plagiarism. They got someone else to write the article. I read it. He copied a lot of the content from my articles on the net, but changed more of the wording. (Mostly so it didn't make sense.)
Is it any wonder we can't find any decent content in the trade press?
............
Other posts: https://community.isc2.org/t5/forums/recentpostspage/user-id/1324864413
This message may or may not be governed by the terms of
http://www.noticebored.com/html/cisspforumfaq.html#Friday or
https://blogs.securiteam.com/index.php/archives/1468
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
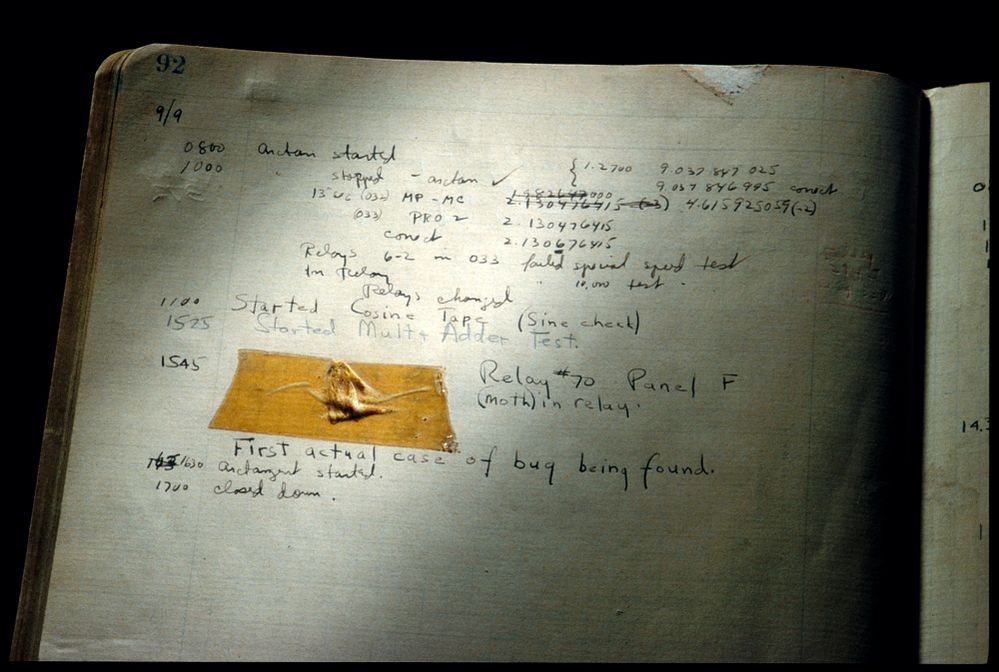
On September 9, 1945, a moth, battered to death, was found in relay 70 of panel F. It was taped into the log book, and the entry noted that it was the "First actual case of bug being found."
It was said to be Grace Hopper who found the moth, in the Mark II computer. Unfortunately, the Mark II didn't come online until 1947. (A commonly referenced photo of the page of the logbook is dated 1947, but after the fact.) And, while Grace Hopper certainly recounted the story of the moth, and the fact that, thereafter, when Howard Aiken asked why the machine wasn't "makin' numbers," he was often told that they were "debugging," there isn't any clear evidence that Grace actually found the bug or taped it into the log book.
It's fairly clear that the moth wasn't the first reference to a bug: the word "actual" definitely implies that the term "bug" was in common use at the time.
............
Other posts: https://community.isc2.org/t5/forums/recentpostspage/user-id/1324864413
This message may or may not be governed by the terms of
http://www.noticebored.com/html/cisspforumfaq.html#Friday or
https://blogs.securiteam.com/index.php/archives/1468