- ISC2 Community
- :
- Discussions
- :
- Industry News
- :
- US Treasury, US SEC, US DOE, Solarwinds, FireEye a...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
FireEye Hacked
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi All
Just to add stupidity to the mix have a look at this piece:
The mind boggles - and probably is having a good belly laugh at the same time:
Regards
Caute_cautim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@denbesten wrote:Coupled with the fact that your CIO is likely already asking if we are amongst their 300k customers creates a great opportunity for a "concentration of power" discussion.
SEC report has the more accurate numbers and possible attack vector listed below.
UNITED STATES SECURITIES AND EXCHANGE COMMISSION
"SolarWinds values the privacy and security of its over 300,000 customers and is working closely with customers of its Orion products to address this incident. On December 13, 2020, SolarWinds delivered a communication to approximately 33,000 Orion product customers that were active maintenance customers during and after the Relevant Period. SolarWinds currently believes the actual number of customers that may have had an installation of the Orion products that contained this vulnerability to be fewer than 18,000..."
"SolarWinds uses Microsoft Office 365 for its email and office productivity tools. SolarWinds was made aware of an attack vector that was used to compromise the Company’s emails and may have provided access to other data contained in the Company’s office productivity tools. SolarWinds, in collaboration with Microsoft, has taken remediation steps to address the compromise and is investigating whether further remediation steps are required, over what period of time this compromise existed and whether this compromise is associated with the attack on its Orion software build system. SolarWinds also is investigating in collaboration with Microsoft as to whether any customer, personnel or other data was exfiltrated as a result of this compromise but has uncovered no evidence at this time of any such exfiltration."
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@AndreaMoore Can you combine this thread with the already created thread please?
https://community.isc2.org/t5/Industry-News/FireEye-Hacked/m-p/41680#M5185
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sounds like network segmentation within the DOE helped out well here but we'll have to wait and see as this develops. I'd also suspect the age of some of those ICS/SCADA systems within the NNSA helped with segmentation as well.
"At this point, the investigation has found that the malware has been isolated to business networks only, and has not impacted the mission essential national security functions of the department, including the National Nuclear Security Administration," Hynes said in a statement. "When DOE identified vulnerable software, immediate action was taken to mitigate the risk, and all software identified as being vulnerable to this attack was disconnected from the DOE network.”
Nuclear weapons agency breached amid massive cyber onslaught
"Microsoft also had its own products leveraged to attack victims, said people familiar with the matter. The U.S. National Security Agency issued a rare “cybersecurity advisory” Thursday detailing how certain Microsoft Azure cloud services may have been compromised by hackers and directing users to lock down their systems."
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
it may be difficult to find information about large scale attacks because the
information gets fragmented. (Come to think of it, that's another security lesson
from CoVID-19: initially, to get all the information, you had to look for stories
about pneumonia, novel coronavirus, SARS-CoV-2, and so forth, before anyone
was talking about CoVID-19 or pandemic.)
Over on the ISC2 "community" ( https://community.isc2.org/ ) there is a fair
amount of discussion about the attack, but it is rather fragmented. There is
discussion of possible privacy implications:
https://community.isc2.org/t5/P/F/m-p/41658
and a question about whether the "supply chain" aspect of this attack means it's a
bad idea to "whitelist" applications:
https://community.isc2.org/t5/T/S/m-p/41766
(Definitely an important question. Whitelisting should be done carefully,
particularly with applications which require pervasive permissions, and, in this
case, it still would have been extremely difficult to detect the attack, since it was
properly signed and authenticated.) Some other discussions on the "community"
have been amalgamated, which might be seen as a good idea, except that they were
amalgamated under the topic title "FireEye Hacked,"
https://community.isc2.org/t5/Industry-News/FireEye-Hacked/m-p/41468
which rather hides the fact that some of them were originally titled SolarWinds
(although nobody mentions Orion), or the fact that it's a developing story about
the Treasury, or attacks by a foreign government. (This is not assisted by the fact
that if you reply to a posting in the "community," your reply does not take the
title of the overall topic, but the specific posting you replied to.)
A few points to make about this specific attack. The first is that it is most likely
part of a much larger campaign. All indications are that the attack is carried out
by a nation-state level attacker, most likely Russia. The importance of it being
part of a larger campaign is that any system found to be affected by this specific
attack must be suspected of having been compromised in other, unknown, ways.
The facts known about the current attack suggest very careful attention to hiding
the existence of the compromise, which, undoubtedly, would also be applied to
other malware or intrusions by the same attacker.
There are, by now, many possible sources of information about this attack, many
very detailed and accurate. Possibly one of the best sources is from the US
government, who have been most concerned with and about the attack:
https://us-cert.cisa.gov/ncas/alerts/aa20-352a and
https://cyber.dhs.gov/ed/21-01/
As a very brief precis of the situation, the attacker managed to obtain credentials
to sign and promote an "update" to the SolarWinds Orion network management
tool. Since Orion requires a high level of access in order to diagnose and manage
network issues, this effectively makes it a Remote Administration Tool (RAT)
which the attackers turned into a Remote Access Trojan (RAT). You will notice
the similarity in the acronyms, which is quite deliberate. Any tool powerful
enough to help you out is also powerful enough to seriously mess you up. Remote
access, even for technical or management support, is a convenience, and
"convenience" is one of the major ways that malware gets introduced and can
operate most effectively.
SolarWinds has about 300,000 customers, but initial indications are that only
about 18,000 systems were seriously impacted. (This still does not guarantee that
the others are safe.) The attackers did appear to be targetting US government
systems. Oh, and FireEye, where they seem to have stolen some attack tools.
Some quick indicators to check for:
- the existence of a file C:\WINDOWS\SysWOW64\netsetupsvc.dll
- any network connections or traffic to a site avsvmcloud.com (This seems to
happen once, and then other connections are negotiated, so you may have to
check traffic back to March of 2020.)
If you are a SolarWinds customer, they are working on updates to remove the
malicious code.
====================== (quote inserted randomly by Pegasus Mailer)
rslade@gmail.com rmslade@outlook.com rslade@computercrime.org
It appears that these hollow toys defied the babies'
expectations, as if they were thinking: There should be something
in there. Which means babies make the mental link between
intentional movement and the requirement for insides. They
already know that this life takes guts.
- Scientific American podcast by Christie Nicholson
victoria.tc.ca/techrev/rms.htm http://twitter.com/rslade
http://blogs.securiteam.com/index.php/archives/author/p1/
https://community.isc2.org/t5/forums/recentpostspage/user-id/1324864413
............
Other posts: https://community.isc2.org/t5/forums/recentpostspage/user-id/1324864413
This message may or may not be governed by the terms of
http://www.noticebored.com/html/cisspforumfaq.html#Friday or
https://blogs.securiteam.com/index.php/archives/1468
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@rslade If you think the threads are fragmented in the Community about this topic, imagine what the FBI 'Crazy Wall' looks like right about now lol!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@rsladeThank you for the great post
https://community.isc2.org/t5/Industry-News/FireEye-Hacked/m-p/41782/highlight/true#M5199
For me, the best part is a link to the CISA document https://us-cert.cisa.gov/ncas/alerts/aa20-352a
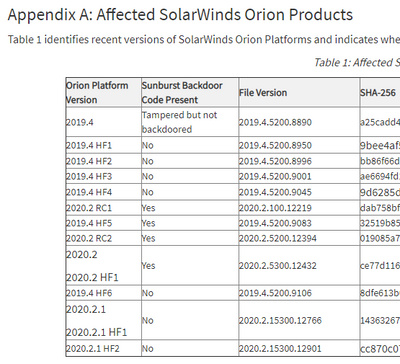
The document has a great table in Appendix A. This table shows the tampered versions of the software and that the current version is not corrupt.
The software 2020.2.1 HF2 2020.2.15300.12901 was released last Tuesday night at 8 PM CST and has been installed globally to update and or rebuild Orion from the ground up.
I take issue with the statement "does not guarantee the software is safe". How does anyone know that any software is safe? The best thing to do is to follow the security guidelines for the software. Here is the PDF
https://www.solarwinds.com/-/media/solarwinds/swdcv2/landing-pages/trust-center/resources/secure-con...
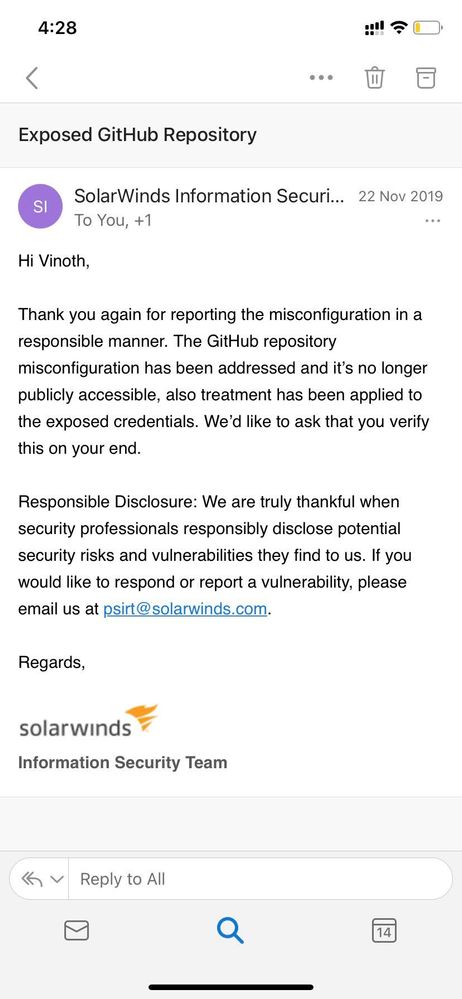
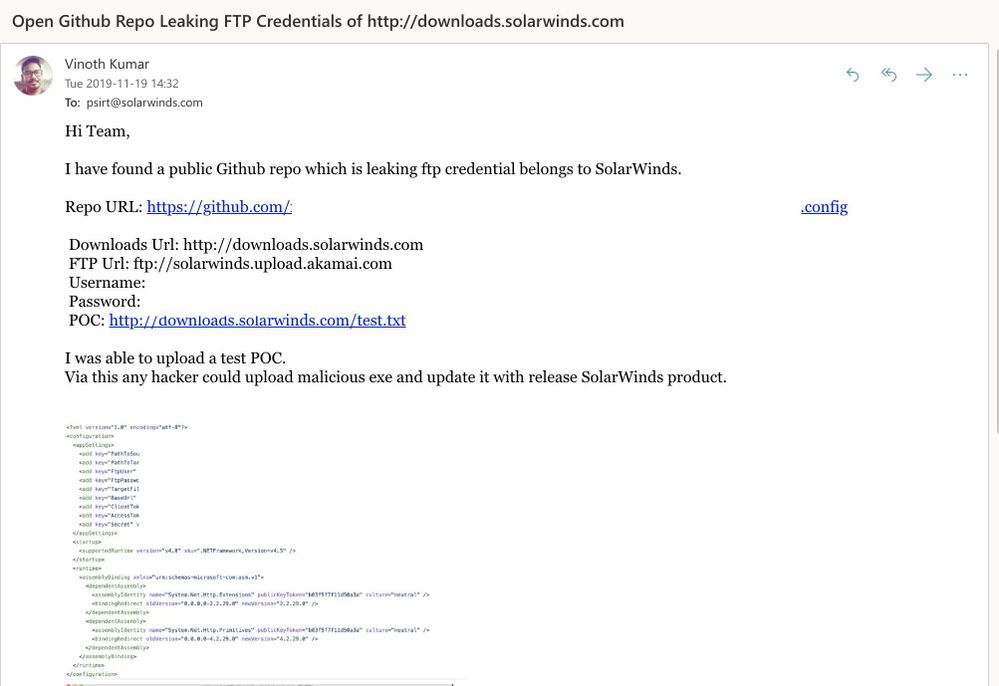
The weak password issue for Solarwinds "solarwinds123" was in November of 2019. On November 11-19-2019 Vinoth Kumar sent SolarWinds an email on the issue. On November 22 Vinoth received a reply that it was remediated. This does not excuse this issue. Every article I read makes it sounds like this was still happening and not a year old.
Looks like a rogue developer set it back in 2019. Most articles on the password issue are clickbaity and lack the facts that this was over a year ago and it was corrected in a timely manner.
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Found a recorded conversation and transcript on the Federal News Network discussing the need for System Security Engineers involved in the development process. Pretty much DevSecOps is what Ron Ross, senior fellow at the National Institute of Standards and Technology, is describing. I like how he breaks down Zero Trust with comparing it to a bad guy breaking into a house.
How SolarWinds could’ve been prevented
"You can have really strong locks on the front door of your house but if you leave the door open anytime during the day, and as you know, bad guy comes in the house and hides in the closet, you can lock the doors at night, and then the bad guy’s in the house. And so you then can have all of your valuables exposed inside the house or you can put a vault in every room in the house. So even though the bad guys in the house, they’re gonna have to go through every one of those vaults and try to get in and that’s very difficult. You can also hang the keys to the vault or the combinations can be posted somewhere in the house."
Seems like a common theme of DevSecOps and Zero trust throughout the different articles for limiting damage in these kinds of attacks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
A great find, thank you - I can also use the analogy describing Zero Trust Security.
Brilliant.
Thank you very much
Regards
Caute_cautim
- « Previous
- Next »