- ISC2 Community
- :
- Discussions
- :
- Industry News
- :
- Re: NIST new ruling on passwords
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
NIST new ruling on passwords
I wanted to see how members on here felt about NIST new draft of password policy suggestion.
What’s new ?
What are the major differences between current received wisdom about “secure passwords” and what NIST is now recommending?
Some of the recommendations you can probably guess; others may surprise you.
We’ll start with the things you should do.
Favor the user. To begin with, make your password policies user friendly and put the burden on the verifier when possible.
In other words, we need to stop asking users to do things that aren’t actually improving security.
Much research has gone into the efficacy of many of our so-called “best practices” and it turns out they don’t help enough to be worth the pain they cause.
Size matters. At least it does when it comes to passwords. NIST’s new guidelines say you need a minimum of 8 characters. (That’s not a maximum minimum – you can increase the minimum password length for more sensitive accounts.)
Better yet, NIST says you should allow a maximum length of at least 64, so no more “Sorry, your password can’t be longer than 16 characters.”
Applications must allow all printable ASCII characters, including spaces, and should accept all UNICODE characters, too, including emoji!
This is great advice, and considering that passwords must be hashed and salted when stored (which converts them to a fixed-length representation) there shouldn’t be unnecessary restrictions on length.
We often advise people to use passphrases, so they should be allowed to use all common punctuation characters and any language to improve usability and increase variety.
Check new passwords against a dictionary of known-bad choices. You don’t want to let people use ChangeMe, thisisapassword, yankees, and so on.
More research needs to be done into how to choose and use your “banned list,” but Jim Fenton thinks that 100,000 entries is a good starting point.
The don’ts
Now for all the things you shouldn’t do.
No composition rules. What this means is, no more rules that force you to use particular characters or combinations, like those daunting conditions on some password reset pages that say, “Your password must contain one lowercase letter, one uppercase letter, one number, four symbols but not &%#@_, and the surname of at least one astronaut.”
Let people choose freely, and encourage longer phrases instead of hard-to-remember passwords or illusory complexity such as pA55w+rd.
No password hints. None. If I wanted people have a better chance at guessing my password, I’d write it on a note attached to my screen.
People set password hints like rhymes with assword when you allow hints. (Really! We have some astonishing examples from Adobe’s 2013 password breach.)
Knowledge-based authentication (KBA) is out. KBA is when a site says, “Pick from a list of questions – Where did you attend high school? What’s your favourite football team? – and tell us the answer in case we ever need to check that it’s you.”
No more expiration without reason. This is my favourite piece of advice: If we want users to comply and choose long, hard-to-guess passwords, we shouldn’t make them change those passwords unnecessarily.
The only time passwords should be reset is when they are forgotten, if they have been phished, or if you think (or know) that your password database has been stolen and could therefore be subjected to an offline brute-force attack.
There’s more…
NIST also provides some other very worthwhile advice.
All passwords must be hashed, salted and stretched, as we explain in our article How to store your users’ password safely.
You need a salt of 32 bits or more, a keyed HMAC hash using SHA-1, SHA-2 or SHA-3, and the “stretching” algorithm PBKDF2 with at least 10,000 iterations.
https://nakedsecurity.sophos.com/2016/08/18/nists-new-password-rules-what-you-need-to-know/
I think this is a great step. The 90 day rotation only made users change the base of their password append with a date or numerical number. Example, TH!S1sMYp2ssw0rd1, THIS1sMYp2ssw0rd2, etc. Once the base of the password was figured out or phished, gaining access is easier.
I still educate my users on passphrases and why they better as a password substitute but our policy (and compliance) rules make it hard to use a nice passphrase.
I have also educated my users on password management solutions. This allows for a long passphrase as the master password that bypasses local policy restrictions. Local solutions work well if you have an office that you will always log into at work. The database for this solution should be stored on a network share for data redundancy. Also, Cloud solutions are acceptable if you have a user who is on the move or never logs in from the same device. I would only caution that your Cloud solution encrypts the data and either you hold the decrypt key or have it part of your master password.
Thoughts?
US Army Veteran - CISSP
It's not a matter of IF but a matter of WHEN. What are you going to do when it happens?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As others have stated, the human behavior aspect of security is going to be a weak spot with passwords written on post it notes or stored in password managers that become compromised. Users that reuse their passwords across accounts is also a huge issue. Enabling and requiring 2FA on accounts should help alleviate the issue and cut down on account compromises. Another tried and true security measure is locking the account after a certain amount of failed login attempts.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In general I like the new ruling, but somthing about "No more expiration without reason" just doesnt feel right.
It shouldn't happen, but we know that users sometimes "share" accounts with each other and that occaisionlly, the leavers process misses an account.
Password expiration is at least a partial control for those events.
As many have stated, 2FA is probably the answer. I don't know why NIST have not mentioned it in the ruling.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Checking the passwords against a list of easily password list sounds like common sense in this day and age
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
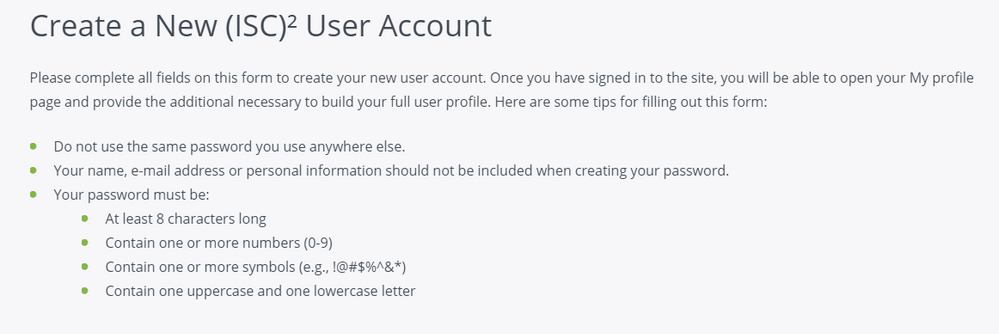
Oh the irony....
I just created my account on here to comment on this post, and when creating my account I ran into this:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Password management is an increasingly burdensome task, for the average user and for enterprise level situations.
I think such frameworks and guidelines are a great starting point...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In January 2017, the French Data Protection Authority (CNIL) is adopting a recommendation on passwords to guarantee minimum security in this respect. It is also providing businesses and citizens alike with practical tools.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I like many of the new recommendations. I've always been a big fan of making password policies user friendly and allowing longer passphrases and elimination of odd requirements. Non-expiring passwords in an interesting twist that I hadn't given much thought to. It seems to be in practice in many banking websites, so I'm curious to see if that continues to take off.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Good for NIST
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Interesting you mention the math about just repeating characters compared to the old "complex" rules @DHerrmann It made me recall the great foundation for that here: https://www.grc.com/haystack.htm
No more arbitrary password aging can't come soon enough in my mind!