- ISC2 Community
- :
- CISSP Study Group
- :
- Forum
- :
- Man in the Middle and TLS
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Man in the Middle and TLS
Hi All,
As per official guide correct answer for below question is C: "Man in the middle". Can anyone explain how attcker will be to read TLS encrypted communication in this case?
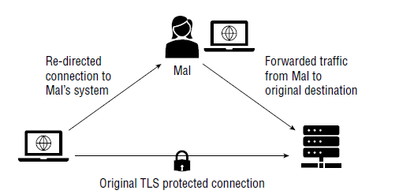
Question : The following figure shows an example of an attack where Mal, the attacker, has redirected
traffic from a user’s system to their own, allowing them to read TLS encrypted traffic. Which
of the following terms best describes this attack?
A. A DNS hijacking attack
B. An ARP spoofing attack
C. A man-in-the-middle attack
D. A SQL injection attack
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's still a "man-in-the-middle" attack, because none of the other answers fit. How it happens all depends on the talents of the attacker.
This Broadcom guide offers a brief suggestion on how such an attack could occur, for reference.
A claim is as good as its veracity.
linkedin[.]com/in/geater
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Sundas wrote:Can anyone explain how attacker will be to read TLS encrypted communication in this case?
MITM/AITM (Adversary in the middle) is a necessary, but not sufficient step. More components are necessary:
- The AITM could keep a copy of the encrypted communications until technology has evolved to break it.
- The AITM could steal the right-side TLS private-key and use it to act as a server on the left side, proxying the communications as a client on the right side.
- The MITM inserts their own CA into the left-hand side so they can issue certificates and proxy as above.
When done by (questionably) good actors, such as the corporate firewall, this is called "SSL Inspection", which is a good term to Google for a deeper explanation.
Many technologies (pinning, stapling, CAA) are being developed to address this risk, with varying success.