- ISC2 Community
- :
- Discussions
- :
- Tech Talk
- :
- Re: Secure DNS missconceptions
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Secure DNS missconceptions
After seeing numerous posts regarding ease of implementing secure DNS, some of them being patently wrong and misleading, I’d like to provide a brief clarification on this subject.
If you’ve read that changing your static DNS entries either on your PC or home router to the one provided by Cloudflare (1.1.1.1) or IBMs Quad9 (9.9.9.9) will provide you with a measure of privacy, these statements are incorrect.
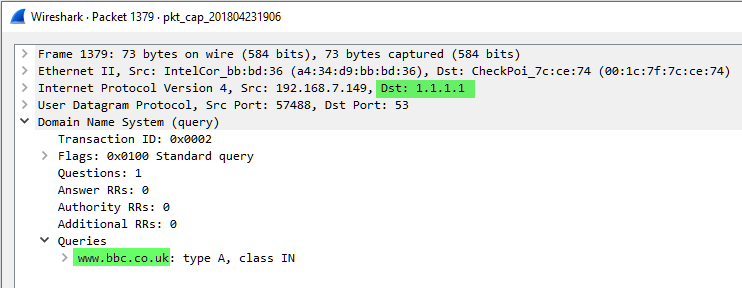
You are simply running unencrypted query to the server(s) CAPABLE of secure communication. Your ISP, hotel, etc. will have no trouble at all collecting, analyzing, and selling your information if all you've done is specified 1.1.1.1 as your preferred DNS. If you are really trying to secure DNS, a bit more work is required.
Cloudflare does provide secure DNS services. It is misunderstanding of how it should be used that I have problem with.
If you simply define static IP as your DNS server, any upstream DNS Proxy will be able to log, intercept and reroute it.
DNSSEC can guarantee that the responses are valid but does not provide confidentiality.
DNS over HTTPS/TLS will do both but could either be blocked by upstream routers/firewalls because it is addressed to known servers (i.e. 1.1.1.1, 1.0.0.1, 9.9.9.9, etc...), or decrypted by MITM, if user trusts its certificate.
The only known good way to assure DNS security is to use DNSCRYPT with DNSSEC. This method using elliptic curve algorithm to encrypt DNS traffic, providing confidentiality and DNSSEC, assuring authenticity of replies.
This last one could be blocked, because you are still limited to the relatively short list of known servers, but you will know that someone is meddling with your DNS traffic.
If you want as close to complete security for DNS as you can get, use IPSEC VPN to a cloud-hosted DNS proxy that you've deployed yourself, that is in turn configured to use DNSCrypt with DNSSEC.
Additionally, be aware that the Windows 10 has, what is known as “DNS leakage”. Regardless of your VPN settings, it is going to broadcast DNS requests in the open to all DNS servers identified on all of its interfaces. I.e. if you are connected to an unsecured Wi-Fi and VPN and both supply your computer with DNS servers, queries will go out of both interfaces, the physical and the virtual and the fastest answer will be used for resolution.
Additional tinkering with the registry required to disable this behavior: https://www.neowin.net/news/guide-prevent-dns-leakage-while-using-a-vpn-on-windows-10-and-windows-8
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What a timely post for me. I have this exact issue at work and your information was very helpful - thanks
L A Jensen
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You are quite welcome!
I'm glad you have found it useful.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for this information. Very helpful!
www.goodsecurityawareness.com
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Vladimir, thank you for sharing your perspective - and even more meaningful to also share a guide to a related fix on Windows 10.
Your comments are valid.
I would add that some folks are altering their DNS not necessarily for misguided (edit: holistic) security perks, but rather for speed. The response time from 1.1.1.1 CloudFlare (or 9.9.9.9 IBM) might on average be a little quicker than default DNS that the user was previously experiencing. This has led some to modify DNS locally on devices, or perhaps configure their home router (or work router).
related youtube video by Linus Tech Tips:
https://www.youtube.com/watch?v=kqnvrjgyEMc
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Both are actually valid reasons: The speed, as you have mentioned, is definitely improves when using Cloudflare, unless your carrier blocking it (AT&T incident, already resolved).
The RELATIVE security factor is also present: if using 9.9.9.9, you are actually better-off from security perspective, as IBM does filter DNS queries using their threat intelligence platform. So the probability of accessing malware-loaded sites or tripping CNC is reduced.
It's the assumption of complete DNS security and privacy specifically, when relying on simple NS configuration changes, that are dangerous.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank-you vt100! I appreciate your post. I've been researching DNS security and auditing and it is definitely a problem area. I've looked at products like Infoblox that mitigate data leakage where the DNS stream is utilized to exfiltrate data. I'd love to see more information in this area.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@rpenner You are quite welcome!
Yes, DNS is the major vector for C&C, data exfiltration and a side-channel communication. Interestingly enough, it was used to some degree for the delivery of the updates in restricted environments by some vendors and, subsequently, by some VPN vendors to circumvent traditional firewalls.
These days, practically all UDP based protocols are being used for nefarious purposes as they are seldom afforded same degree of scrutiny as TCP.
Traditional firewall vendors do not like to tackle DNS, as it directly impacts listed performance of their appliances and are often limiting their threat prevention for DNS to a subset of common exploits.
From the point of view of performance and security, cloud-based DNS specific security solutions are probably the best at addressing these issues.
Common names in that area are the OpenDNS (now Cisco Umbrella), TitanHQ and Infoblox Active Cloud.
- « Previous
-
- 1
- 2
- Next »