- ISC2 Community
- :
- Discussions
- :
- Tech Talk
- :
- NIST SP-800 control listing
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
NIST SP-800 control listing
Hello Everyone!
I found difficulty to understand how controls are laid out in NIST Special Publication 800-53. I mean, elements of a control listing (e.g. Priority , baseline allocation etc.) Could someone suggest any relevant reference /book /document which explains the documentation for a rookie.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am not certain that I understand where you are having difficulty, however, based on your question, I believe the issue is that many people tend to look at SP 800-53 as a stand alone document as opposed to one of the component documents support the NIST Risk Management Framework (RMF). To get a better understanding of where 800-53 fits into the RMF I suggest reviewing SP 800-37 "Guide for Applying the Risk Management Framework to Federal Information Systems: a Security Life Cycle Approach"
The baseline is derived by completing the system categorization (FIPS 199 & NIST SP 800-60) to determine the sensitivity levels for a systems Confidentiality, Integrity, and Availability (CIA). using the appendices of the 800-53 or the "Minimum Security" section on the 800-53 webpage: https://nvd.nist.gov/800-53/Rev4.
Unfortunately, I am unaware of any books I would recommend to summarize these documents and supporting processes. IF you have the patience to read through them, the NIST documents do a good job, but tend to be very wordy and repetitive.
I hope this information is helpful, if not I will be happy to clarify anyplace I can where I misunderstand your concerns
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
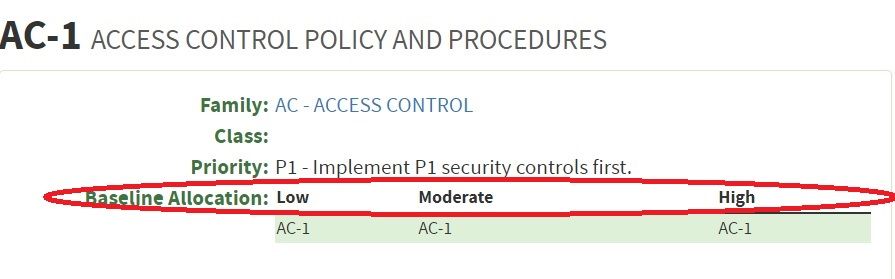
It helps me for sure, the link provides good info.I Thank you for your time and info. Just in case please give me a clue to understand the baseline allocation element purpose in the snap below
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
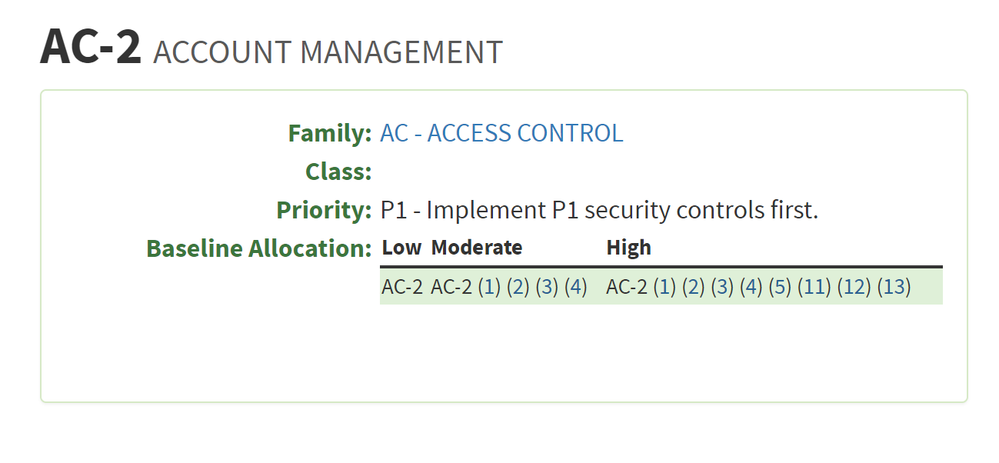
@iluom, the baseline implies the minimal recommended settings depending on the level you opt for. You use this as a starting point, and then tailor the control requirements depending on your situation.
Let's illustrate this with the A-2 (Account Management) control, shown below:
For a Low level, it's the basic set of controls, but higher levels have enhanced controls. Nonetheless, no level has A6, A7, A8, & A9, given that they may have dependencies, the costs of implementing them may outweigh the benefits, they may not be needed in an environment, etc.
In the example that you provided, there are no enhancements, so they've referenced just the main control for all the security levels, since there's nothing more.
For other controls, such as A-6 (Least Privilege), you'll notice that there's nothing provided for the Low level & both the other levels have all the enhanced controls.
Whatever the case here, you start by selecting a particular control and the level you want, and then go on to add or remove controls to meet you own needs.
CISM, CISSP
www.linkedin.com/in/shannondcruz
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Awesome!!
Thank you.