- ISC2 Community
- :
- Discussions
- :
- Tech Talk
- :
- Finding weak encryption
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Finding weak encryption
I'd be interested to hear from anyone who has faced the following problem, particularly if you managed to solve it.
Imagine a large, complex, mixed network containing a lot of hosts running Windows and various Unix derivatives. As time wears on they get out of date so the company has a significant rolling upgrade programme. Some (many!) older hosts have deprecated security protocols and cipher suites so the natural thing to do is to modernise these, though we have also to re-enable the old protocols/ciphers because the hosts with which they communicate aren't yet upgraded and capable of modern encryption.Sooner or later we have a very much messier protocol/encryption estate. The details of which encryption method is enabled for which purpose is beyond the scope of the CMDB, so the task of going through the estate to disable unused, weak encryption methods becomes a challenge. Trial-and-error isn't a great idea because there are many services for which even a brief outage cannot be tolerated. It looks as though the way forward will be to determine by inspection which hosts are using which protocols, and for what purpose - this will then provide a baseline from which to work to disable the weak ones as the hosts/applications depending on them are upgraded.
Finding out which protocols are enabled on listeners is quite straightforward - any halfway-decent scanner can do that. The hard bit is finding out which ones are in use. One way would be to scan the estate to build a list of hosts that have weak encryption enabled and then, for each host, run a pcap and/or examine logs to determine whether it is using them and, if so, for what purpose. That will generate a list of the real pain points.
Is there a better way?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
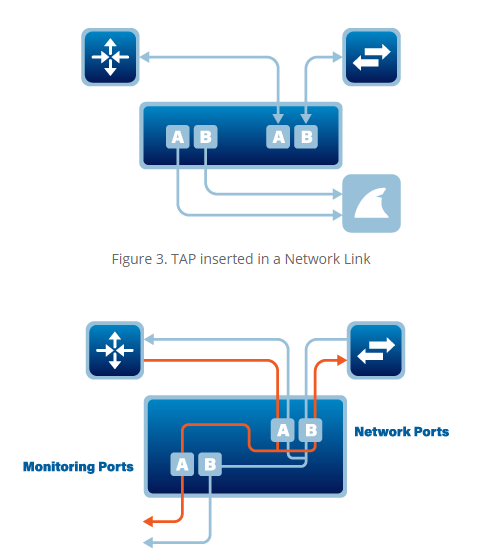
Was the plan to use a network tap close to your layer 3 device and copy network traffic to an endpoint device that has Wireshark or another PCAP program running? I'm not sure of a better way to see if each legacy device is actually using the old encryption standard but I'd still conduct the port/vulnerability scan regardless.
What Are Network TAPs? And Why Do We Need Them? (profitap.com)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, Michael.
For sure we'll stilll be scanning - we have a continuous scheduled scan programme anyway, so we can trawl the current data for weak encryption alerts.
Regarding the network tap, we'd do something like that, though the details will vary depending whether it's a single physical host or a guest in a Hyper-V, VMWare or LPAR farm. In principle (and assuming a beefy enough machine running the capture) we could SPAN a server VLAN and quite possibly pick off several endpoints at once. There might be an awful lot of data to masnage if we do it that way, though!