- ISC2 Community
- :
- Discussions
- :
- Industry News
- :
- Payment card Security updates & news
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Payment card Security updates & news
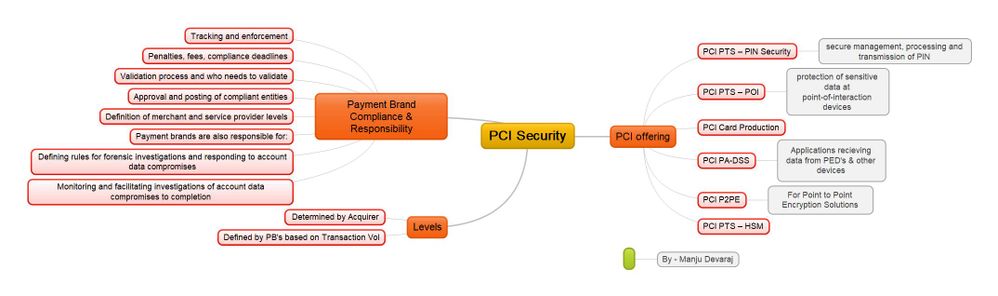
Find all answers to security requirements from Payment Card industry , new updates , releases & changes from Payment Card Industry .
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Anybody else wrestling with the deprecation of SHA1? We just successfully completed an application change that allows the matching hash algorithm to be client-specific, via configuration, as a key step toward conversion - so that we could convert one client at a time. Lot’s of clever ideas brought together by the team to minimize disruption on a massive update of these key matching fields.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sounds Good , most of the trusted browser deprecated the use of SHA-1 support . Test your SSL using the below to understand the Grade of your SSL , supported cipher suites .
https://www.ssllabs.com/ssltest/index.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do share one the best ideas that you feel was really great , one which really simplified the journey of migration from X to Y .
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Two key ideas minimized disruption. The core application functions that hash card numbers were modified to take a new parameter - which hash algorithm to use. (We had some older clients using a hard coded SHA1, and some newer clients using a hard coded 256 - on a “Version 2” core code base).
With each client’s new parameter set to the existing value (SHA1 or SHA256), the code change was launched (2 lines of code: 300+ test cases) but ... no data was changed. We did this so that we could “flip the switch” (to 512) one client at a time. It took a couple of hours of down time (2 am - 4am) to validate the code changes, but - at least - no data updates were needed now.
The actual conversion of each client (one at a time) took less than a minute of down time, accomplished by precomputing a completely new table, and doing a table rename along with the publish of the parameter change.